2 factor authentication: a closer look
2 factor authentication is an additional security system used to confirm a user’s identity. It is used to access websites or online services and guarantees inviolable protection, thanks to the different types of verification required.
Enabling this extra security measure in order to protect your account is often optional, but strongly recommended. The excellent protection it offers against breach attempts is sufficient to justify spending a few extra seconds on the additional requirements during access.
Types of authentication: single and multiple factor
Generally speaking, in order to access any digital system (computer, cashpoint, website or online service), the user must identify themselves by entering their username and password (or PIN). This is known as one factor authentication, as it requires just one word or number.
With two factor authentication there is an additional request, which could involve a ‘possession’ factor (a physical thing that the user possesses, such as a smartphone, security token etc.) or ‘Inherence’ factor (something unique to them such as a fingerprint, face scan, tone of voice etc.)
A typical example of a ‘possession’ factor is a code received by SMS or email when you open your email inbox on a different device. Most providers offer the option to enable 2FA (2 factor authentication) using this system.
‘Inherence’ on the other hand, is based on verifying unique biometric data belonging to the user. Some home banking sites for example, require banking transactions to be confirmed with a fingerprint on the smartphone or a face scan.
In certain settings, where extremely sensitive data is handled, 3 factor authentication may be found, incorporating all three methods mentioned above in order to access the system.
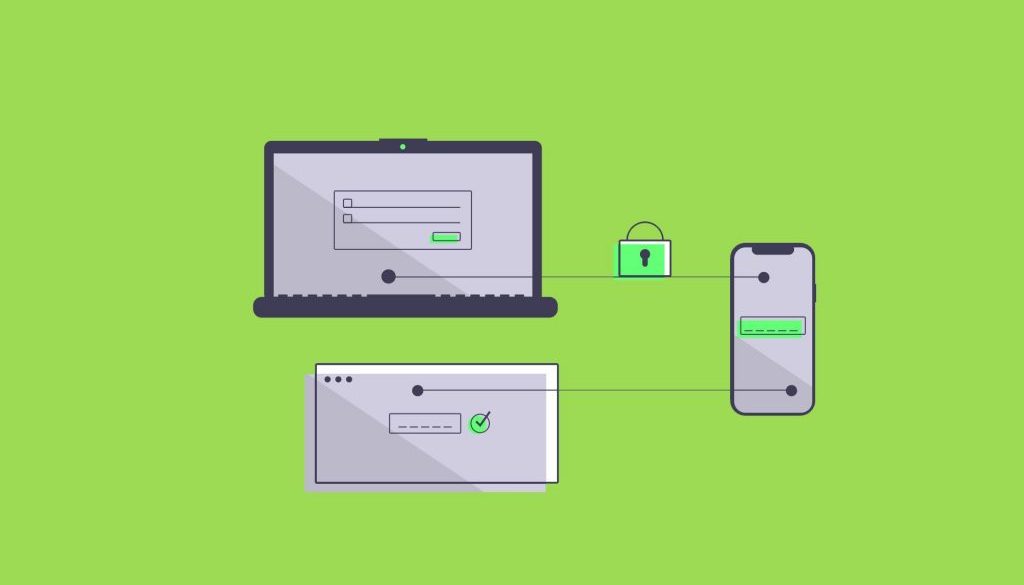
How 2 factor authentication works
If web portals or apps offer the option to activate 2 factor authentication, it is always best to activate it. It is a straightforward, clearly structured procedure, which is highly intuitive and requires just a few seconds more than the usual login with password.
Once you have entered your credentials in fact, you receive a confirmation request of the second identification factor. As mentioned above, it may be a code (received by SMS, email or specific app) or a biometric check. Once you have satisfied the second request, access to the service is guaranteed.
The main advantage of this additional code is that it is something unique and inviolable, possessed exclusively by the user. This ensures that, in the case of violation of login details, nobody can gain access to data unless they have access to the specific smartphone or other device used in the 2 factor authentication process.
Online security is never too much
Some people are sceptical about adopting this defence method with its additional request during the login phase. It should be noted however that passwords alone are not sufficient to guarantee an acceptable level of security, even when they are long, complex and varied.
The number of websites falling victim to data breaches continues to increase daily and this translates into thousands of users having their login details stolen. Bearing in mind that when an account is hacked, this is not necessarily due to user error, it is essential to put in place a second line of defence capable of restricting access.
Translated by Joanne Beckwith