Smishing and Vishing: the evolution of spam
The terms smishing and vishing refer to two variations of the more well-known phishing: a type of IT attack, aimed at stealing the victim’s sensitive data. Although the objective and method remain mostly the same, these techniques employ different means of communication.
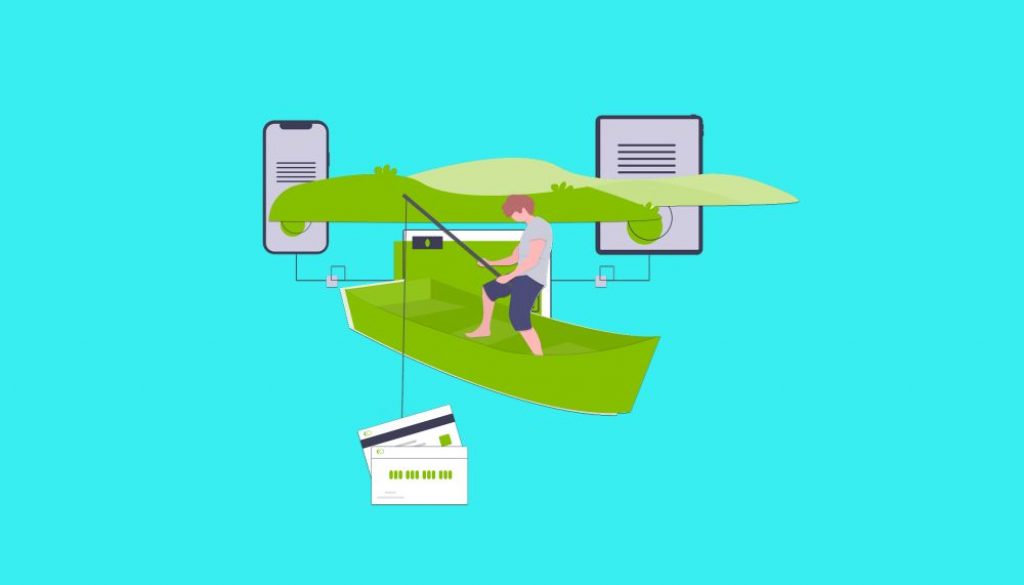
In the case of phishing, the attack is launched via the sending of an email containing a link or malicious attachment. Smishing, however, involves the use of SMS (from where it gets its name, an abbreviation of SMS Phishing), while vishing uses voice calls (Voice Phishing).
How smishing and vishing attacks are structured
A typical feature of phishing attacks (also used in smishing and vishing), is the tone used in the message, whether written or spoken. The content of the message is created ad hoc to give the user a sense of urgency, by, for example, alerting them to possible breaches of their personal data, or warning them of steps they must take in order to unblock payments.
This kind of interaction transforms the victim’s psychological state into one of anxiety and encourages them to reveal sensitive data in order to resolve the matter as quickly as possible. As well as the message itself (either written or voice), with smishing and traditional phishing, there are always some links or attachments to download.
Usually, when the user clicks on the link, they are redirected to a fraudulent copy of a well-known home banking or telecommunications website for example. Then the unfortunate victim is asked to fill in an online form with their personal details and this is how their sensitive data such as passwords or credit card numbers are stolen.
In the version where an attachment is sent, the message includes instructions explaining that an application needs to be installed in order to complete the requested procedures. When the user downloads and installs the app however, they are opening up their smartphone to the cyber criminals and allowing access to viruses or malware which retrieve sensitive data from the device, without the user realising.
There is also another type of malevolent software installed via an attachment, which is able to create a backdoor into the device. This ensures remote access for the IT pirates, who can even infiltrate the victim’s domestic network through WiFi.
Vishing is also characterised by the urgent tone of the messages, but it is programmed to create a believable simulation of a phone call with a human interlocutor. In reality, the victim receives a call from an automatic recording device, which, also in this case, asks them to reveal sensitive data.
How to protect yourself against smishing and vishing
Considering that the modus operandi used in smishing and vishing are basically the same as in the better-known phishing, protective measures are similar. As for smishing, the security rules are similar to those designed to protect against malicious emails:
- Avoid installing apps, especially those from unknown sources;
- Never click on links included in an SMS;
- Pay careful attention to the identity of the sender and the way the message is written (grammatical errors or convoluted sentences are signs of a potential scam):
- Protect your device with specific software certified as anti-malware and anti TimpDoor;
- In the case of company phones, limit the installation of applications by employees and create virtual encrypted containers for the storage of sensitive data.
In the case of vishing, it is essential to bear in mind that no bank or other company will ever ask for sensitive data by phone, especially not using a pre-recorded message. The important thing is never to provide any kind of information if you are not completely sure of your interlocutor. Furthermore, it is best not to dial any strange numbers if you find a missed call.
Translated by Joanne Beckwith